Lista 96+ Foto ciberdelincuencia robo de datos e identidad y fraude El último
¡Descubre las increíbles imágenes de ciberdelincuencia robo de datos e identidad y fraude en huanluyenantoan.edu.vn! Este sitio web ha recopilado cuidadosamente y elaborado una selección de imágenes. Además, hay más imágenes relacionadas disponibles en . ¡No te lo pierdas!
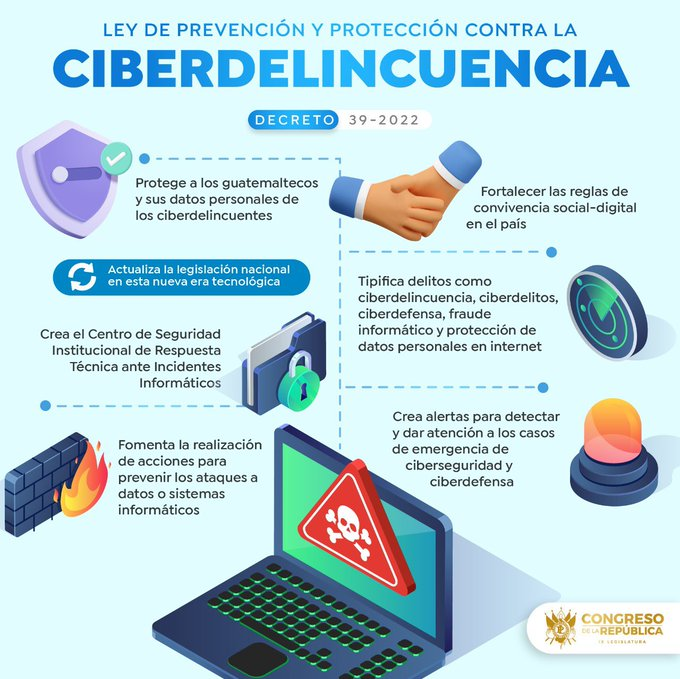
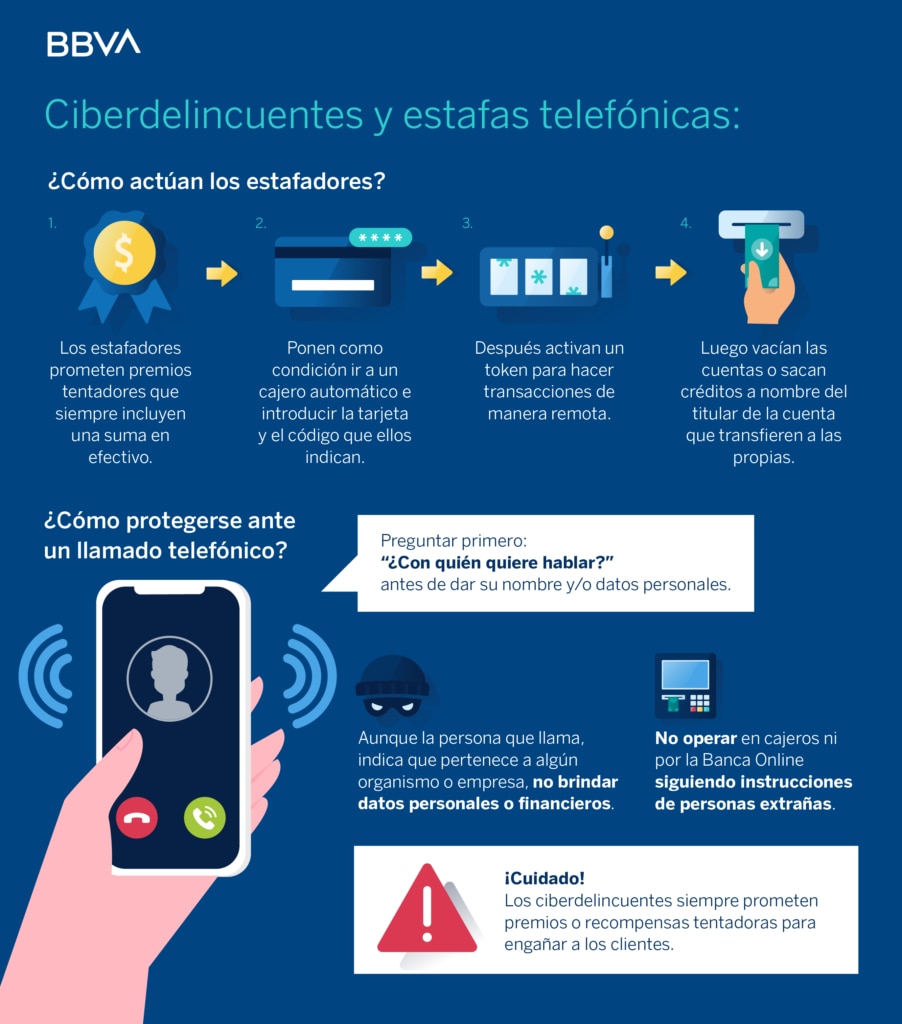
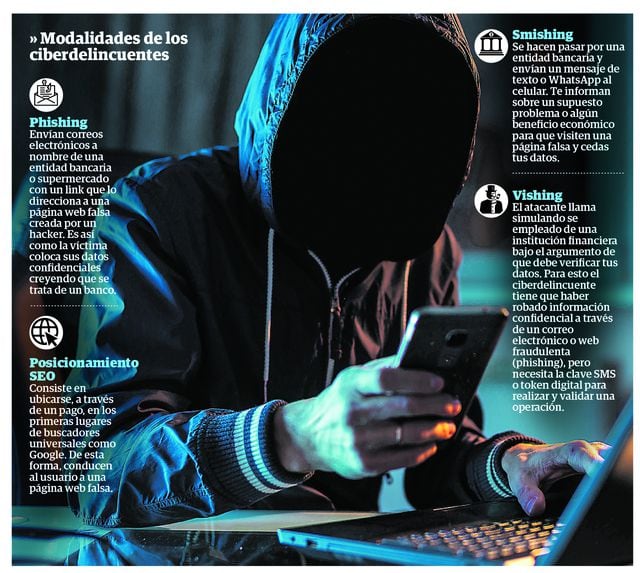
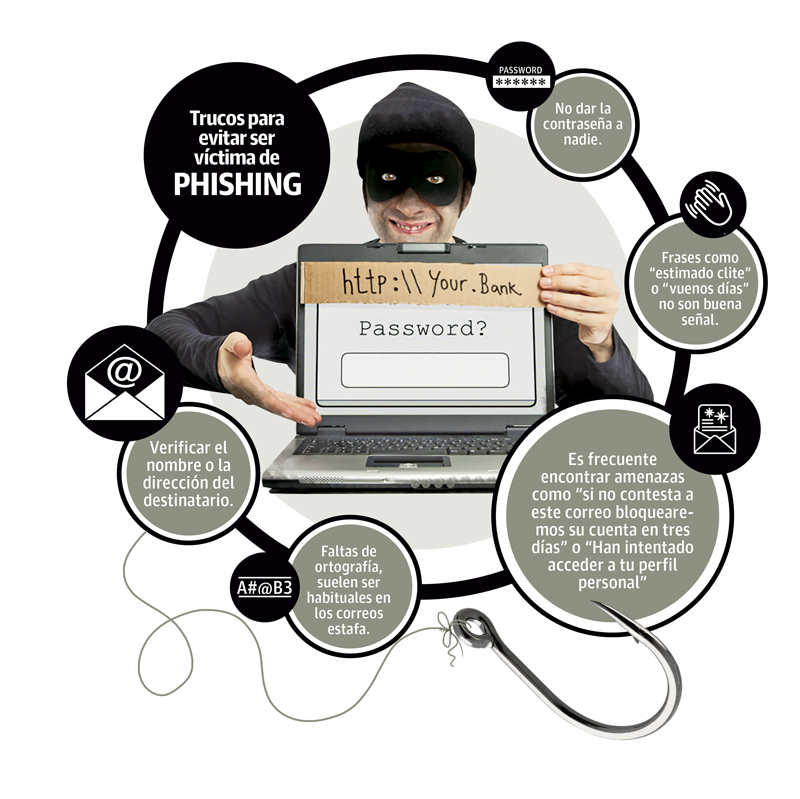
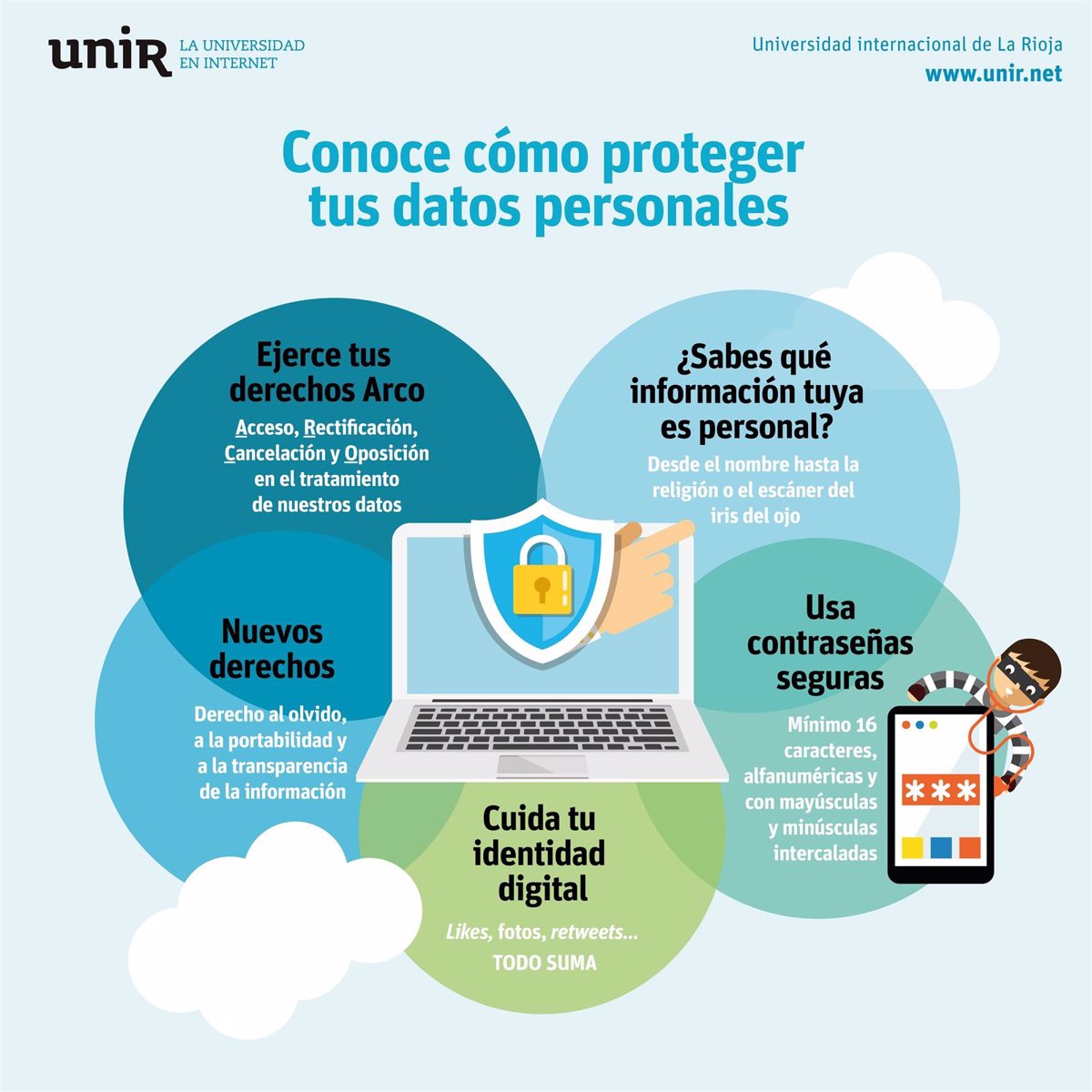
ciberdelincuencia robo de datos e identidad y fraude









































































.png)









Posts: ciberdelincuencia robo de datos e identidad y fraude
Categories: El álbum
Author: huanluyenantoan.edu.vn